The first tool Microsoft produced for remotely deploying Windows on client computers throughout a network was called – in classic Microsoft-ese – the Automated Installation Kit (AIK). What made it relatively versatile was a feature introduced with the Vista kernel called ImageX, that enabled a complete, working image of the operating system to be “painted” onto any hard drive, locally or remotely. This was so much better having to generate each new component through the classic Setup process we all know and hate; and later, the Microsoft Deployment Toolkit took over this task.

The next generation of Microsoft’s remote installer, called Windows Intune, has been in beta since last March; and as we learned yesterday, will move to general availability (GA) on October 17.
Besides having a much nicer name, Microsoft’s next remote installer console goes into far greater depth than its sorry-acronym predecessors. Unlike AIK or MDT, Intune is browser-based, and can manage deployments on clients remotely through the Internet as well as the local network. It offers deployment support for third-party software. And the deployment agent – the thing that actually installs the software – is moved off of the company network and onto the Windows Azure platform.

The console is Silverlight-based, so it should not require Internet Explorer. The Managed Software workspace, shown here, can deploy supported software packages to any of the managed computers that are signed up with Intune. Keep in mind, this is all about your Intune circle, not just your corporate network. Each piece of managed software represents an installation image that you create yourself. Adobe Reader X shown above may be a bad example since there typically isn’t much there for you to configure. However, software that supports Microsoft’s ImageX deployment mechanism will let you install it on a prototype computer, configure it as you will and load it with options (for instance, company templates for Office), then capture an image of that software and deploy it multiple places.
That may seem wrong and even illegal, but it all works out in the end. Once this remote system deploys the image, the enrollment process takes place for each user separately. So licensing matters are all straightened out on startup.
What does not work anymore – at least not for Intune – is the notion of creating multiple images of the operating system plus applications, each one configured differently, storing those images in a colossal repository, and remembering which one is the right one for a particular class of client. Microsoft called that process thick imaging, and with Intune, it’s now a no-no.
In its place comes thin imaging, which mandates that there be one master image of the operating system, and separate images of applications which can be updated as necessary.
As online documentation currently reads, “In this process, you install the default Windows image, and then automatically install required applications immediately afterward. Both MDT 2010 and System Center Configuration Manager make this process easy. The benefit is that thin imaging reduces image maintenance and image count considerably. Updating an application no longer requires capturing a new image. You simply update the application in the deployment share.”
Intune monitoring clients must still be installed on remote systems, and this process still requires MDT or SCCM.
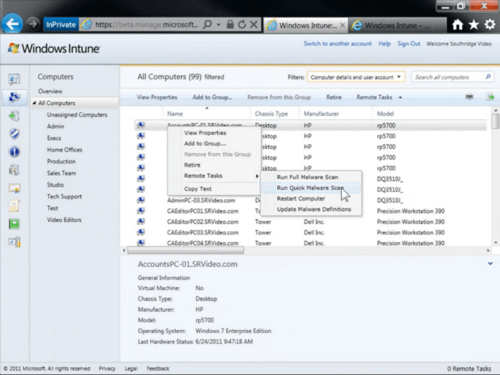
In what could be a glimpse of the future for Microsoft management tools, Intune adds a feature that lets managers run a few security scans on remote client systems – in this example, running a malware scan. If admins can do something like this remotely, there’s a number of other System Center-centered tasks that admins might like to see moved to the Azure platform as well.
After all, as Intune program manager Alex Heaton pointed out on his company’s own blog earlier this week, “Businesses need to ensure that PCs are highly secure and well-managed to help protect corporate data and assets, reduce support calls and streamline the cost of delivering routine management and security.”