
What do you call an organism that thrives off the misfortune or mistakes of another?
A lawyer.
Here’s another term that works: parasite. And when it comes to the marketing and communication of Internet and Web-based security products, that is an apt metaphor.
Think about it. If you are a security company, what is the best way to show that your product is not only needed, but absolutely necessary? The answer of course is to help create a world where bugs and cyber-vulnerabilities make headlines on a daily basis. To highlight those bugs and vulnerabilties and position your product as the best way to keep your information and your company and your equipment safe.
Since before the advent of the Internet, security companies have used these scare tactics to drum up business for their products. It is a familiar cycle: Issue a press release highlighting research about security flaws in applications and websites and then say, “Keep yourself protected with our top-of-the-line product.” It must be a highly effective form of marketing because security companies continually rely on it.
Zscaler Drums Up Fear About ESPN App
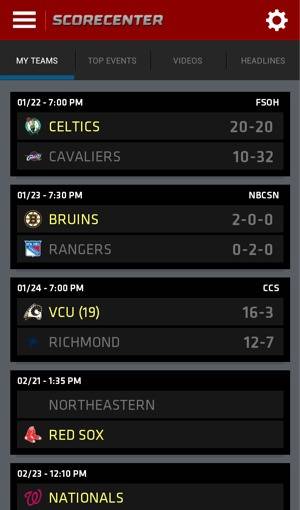
The latest perpetrator is San Jose-based Zscaler. Last week, two different public relations professionals bombarded my inbox with the exact same story: ESPN’s ScoreCenter app has XSS vulnerabilities and sends users’ passwords over plain text, making it simple for any malicious hacker sniffing for attainable user information easy to intercept.
Great, I thought. ScoreCenter is one of my favorite apps and one of the most popular sports apps in Google Play and Apple App Store. I should consider passing this on to our readers, many of whom no doubt use the app. But I had a few questions first.
Foremost, did Zscaler reach out to ESPN before pushing its press release? Because, you know, this is probably something that the app developers at the world’s largest sports network would probably want to know about as soon as possible. Or did Zscaler go with the “publish first, deal with the consequences later” approach?
After two attempts to reach Zscaler’s PR representatives on the question, my emails remain unanswered.
But here’s the rub. It does not benefit a company like Zscaler to tell app publishers of vulnerabilities much ahead of time. If the affected company moves to fix the bug, there is essentially no bad news to drum up fear and push users to the security product that will “fix” the issue.
Zscaler began pushing its PR campaign on January 16. It published its report on January 17 and by January 18, ESPN had fixed the app. Whether or not Zscaler told ESPN about the vulnerability before publishing the news remains unanswered. An XSS vulnerability is not a difficult fix for most developers and is usually the result of an oversight by the programmers.
Update: Michael Sutton, VP of security research at Zscaler got in touch with ReadWrite after publication of the article to say, “I’m concerned as you suggest that we didn’t inform ESPN of the vulnerabilities ahead of the release of our blog and that is absolutely not the case. We did work with ESPN and they were great to work with.”
Somebody Smell A RAT?
But Zscaler is far from the worst culprit in this area. One of the most prominent scare mongering campaigns in recent memory played out in August 2011. Security firm McAfee used style magazine Vanity Fair to announce one of the largest and most persistent viruses in history, dubbed Shady RAT (Remote Access Tool). Why Vanity Fair? Because it is a trusted publication read by many people and one that many people that are not extraordinarily tech savvy read. The target is the consumer that McAfee can scare into buying its product because they do not know any better.
This was well before McAfee’s founder’s well-chronicled flight from authorities in Central America, but involved a similar level of head-scratching.
And that was not the first time that MacAfee had run a scare-tactic PR campaign. In 2011 it had Operation Night Dragon and Aurora. These were tied to varying bugs in Internet Explorer as well as spear-phishing social hacks. If anything, McAfee as a company loves to make a big splash.
Zscaler is not quite as aggressive as McAfee, but its PR team is very active in making sure that people know of vulnerabilities that its ZAP product can fix. In the past seven months or so, it has warned that, “10% of mobile apps leak passwords and user data;” “80% of Olympic domains are scams and spam;” and “apps downloaded by 185 million are vulnerable to attackers to obtain bank info.” Each time, Zscaler conveniently had a product to combat the problem.
A Responsibility To Be Responsible
Unlike some conspiracy theorists, I am not accusing security companies of actually creating the bugs and viruses that they then sell their product to consumers to protect against. Malware happens and there are bad actors in the world who want to steal your data – and your money. Security products can help protect you from them, if you can figure out exactly which product fits your needs.
The problem is that many security companies seem more interested in frightening headlines, scaring the crap out of consumers for customer acquisition and being known as the company that found notable viruses, bugs and vulnerabilities than in actually protecting consumers from the most dangerous and widespread threats.
For an industry that is supposedly all about Internet responsibility, too often, the marketing and communications departments of security companies are anything but.
Top image courtesy of Shutterstock.

















