One of the popular ReadWrite posts discussed the 6 emerging cyber threats to look out for in 2019. These threats call for more robust security tools and strategies to protect our data.
Also, the rapid rate of advancement in cyber threats deems it necessary that we constantly adapt to developments in the cyber world. Browser extensions belong to the group of tools brought about by technological innovations. These tools, though often overlooked, should be put to use on a daily basis.
There are a whole lot of extensions out there for productivity, customization, shopping, games, and more. They can modify the user interface, block ads on Web pages, translate text from one language to another, or add pages to a third-party bookmark service such as Evernote or Pocket.
Oftentimes, your job will determine the type of extensions you’ll have installed. As an online marketing consultant, I have loads of website review tools installed, alongside security tools like UrbanVPN free extension. These extensions make my work a whole lot easier and protect my devices.
Some extensions help to ensure swift activation and unlimited bandwidth that allow you to stream and download content with ease and speed.
Popular web browsers such as Chrome, Firefox, Safari, Opera, Internet Explorer, and Edge support extensions. These extensions are readily available with some more helpful than others.
4 Popular Free Extensions and the Important Roles They Play
A browser extension is a lightweight software application that can extend your web browser with additional features, modify web pages, and integrate your browser with the other services you use.
The beauty of these extensions is that quite a handful of them are free. Let’s take a look at these five popular free extensions and the important roles they play.
-
Grammarly
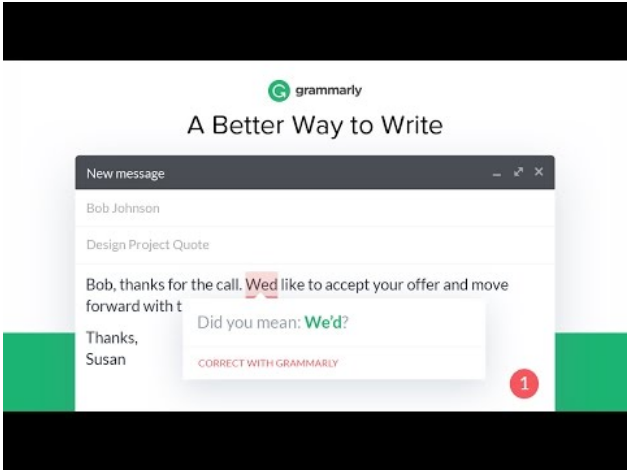
Grammarly ensures all your messages, documents, and social media posts are clear, mistake-free, and impactful. Adding Grammarly to Chrome means that your spelling and grammar will be vetted on Gmail, Facebook, Twitter, Linkedin, Tumblr, and nearly everywhere else you write on the web.
Once you register your new account, you will start to receive weekly emails with personalized insights and performance stats. You can create and store all of your documents in your new online editor.
-
UrbanVPN
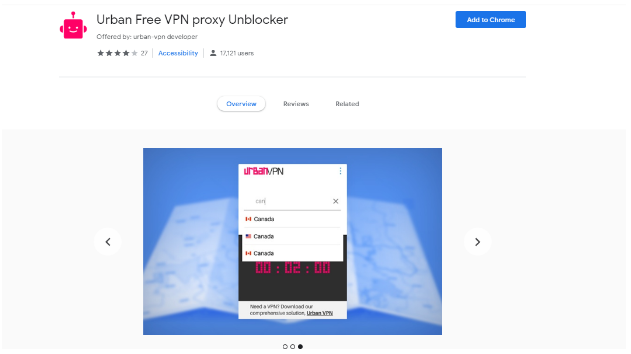
Urban VPN is a subsidiary of Urban Cyber Security and the creator of one of the most reliable and secure, free, virtual private networks in the world. Urban VPN Browser Extension offers you quick and easy activation and unlimited bandwidth.
It keeps your browser activities safe and private, protects your browser from harmful advertising and protects your device from malware and other vulnerabilities when using public Wi-Fi connections. Urban VPN allows you to surf safely without fear of personal information theft, among other security risks.
-
Avast SafePrice
Though online shopping reduces the stress you have to go through any time you want to purchase a product, it did not completely eliminate the stress.
The free Avast SafePricce browser extension, however, has totally eliminated this problem. You can now find the best prices, deals, and discount coupons while shopping online with the price comparison and coupon extension by Avast.
Once you’ve installed the extension, just search for the item you’re looking for on any online store. Avast SafePrice then automatically checks every other trustworthy, reputable shopping website and gives you a comprehensive list of the best online deals and free coupons.
-
FlowCrypt
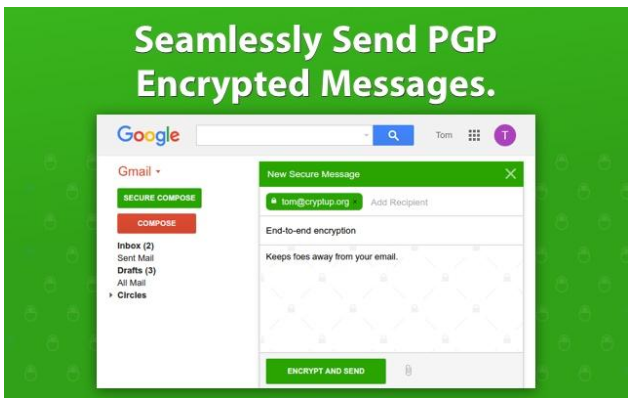
FlowCrypt adds a Secure Compose button to Gmail and G Suite. This way, you can send private PGP encrypted emails when you choose to. The extension lets you use PGP end-to-end encryption by generating a private and public key.
File encryption is also fully supported. You just open a compose window in order to encrypt an attachment, then add the recipient’s private email, and attach a file.
Potential Threats Surrounding Browser Extensions
-
Malicious extensions
The very first thing is that extensions can be outrightly malicious. This is found mostly with extensions that come from third-party websites, but we may also have situations where malware sneaks into official markets as well as in cases with Android and Google Play.
For example, security researchers in 2018 uncovered four malicious extensions in the Google Chrome Web Store. It was not a case of isolation as there were reports that in late July and early August of 2017, unknown attackers compromised the accounts of at least two Chrome extension developers. The criminals then used their unauthorized access to automatically install extension updates that injected ads into the sites visited by users.
Later in August, Renato Marinho, who is the chief research officer of Morpheus Labs and a volunteer at the SANS Institute, uncovered an elaborate bank-fraud scam that used a malicious extension in Google’s Chrome Web Store to steal targets’ passwords.
An extension is not supposed to do that but the problem is that only Google Chrome requires permissions among the commonly used browsers, and users are usually powerless to do anything about it.
Even basic extensions usually require permission to “read and change all your data on the websites you visit,” which gives them the power to do virtually anything with your data. And if you don’t give them that permission, they won’t be installed.
-
Hijacking and buying extensions
Most times, users download harmless extensions, which are automatically updated. Hackers are aware of this fact and as a result of the massive user base which they find inviting, they easily upload malicious extensions without the knowledge of the user.
Ethical developers usually don’t do such things but these crooks often hijack their accounts and malicious updates can be uploaded to the official store on their behalf. That’s the scenario you have any time hackers use phishing to get access to the credentials of developers.
Crooked developers, on the other hand, when approached by malevolent companies that offer to purchase their extensions for a handsome sum cave in. Extensions are pretty difficult to monetize, hence, some developers sell out without minding the consequences.
Such companies, after purchasing the extension, go about updating it with malicious features and contents. Invariably, the malicious updates are pushed to users.
That was the case for Particle, a popular Chrome extension for customizing YouTube that was abandoned by its developers. The company that bought it over converted it into adware.
-
Dangerous but not malicious
There are some extensions that are not malicious but dangerous. The danger arises because most extensions have the ability to collect a lot of data about users.
Sometimes, these data are not incognito enough, which can cause serious privacy issues. The parties that purchase the data can identify the users of the plugin.
Web of Trust, a once-popular plugin for Chrome, Firefox, Internet Explorer, Opera, Safari, and other browsers encountered this problem. The plugin was used to rate websites based on crowdsourced opinion as well as collecting the full browsing history of its users.
Rounding it up
Despite the fact that extensions can be dangerous, some of them are really useful and that’s why you probably wouldn’t want to abandon them completely. It’s advisable to download and activate trustworthy extensions like the ones discussed above.
With browser extension features such as hiding your IP address and browser history, it’s a fact that when discussing ways to unblock websites and access unlimited contents online, browser extensions are definitely one solution that can’t be overlooked.
Still, the risks of browser extensions are quite real. Security awareness training which is highly recommended must stress that users should never install unknown extensions.
By allowing uncontrolled installation of arbitrary plugins and extensions, you increase a network’s overall attack surface and leave users and networks open to infection and data loss.




































