In theory, security researcher Charlie Miller was just trying to help. Apple’s iOS is probed by malicious hackers constantly. They want a way in. To this point, Apple has been successful in keeping them out. It is one of the values of its iron fist rule over the App Store and the iOS user experience. Miller found a way in and planted a sleeper app in the App Store that he was going to use to present the security flaw at a conference in the coming weeks.

In planting the malicious app, Miller violated Apple terms of service and has been suspended from the iOS developer program for a year and his app has been removed. What the app did was get around the code signature requirement for iOS apps and allowed the app to connect to a command-and-control server to download additional code to the application.
Does Miller’s exploit sound familiar? It should, because that is essentially the tactic that has been used multiple times with malicious Android applications. The goal for malicious hackers is to do two things to a mobile device: get kernel access and allow the app to speak freely with a C&C server. That way additional code with a different set of permissions can be downloaded and the hacker can take control of the device.

The code signature is like an electronic ID from the makers of an app. In Android, security apps scan for the code of an app and can then choose to white or black list an app or publisher from there. That has never really been a problem with iOS because no app could function without an approved signature. What Miller did was find a part of the iOS browser that was allowed to run without a signature (which, according to Forbes article on Miller’s research, was used to accelerate Safari’s speeds). Miller then exploited that exception to allow his own app to contact the C&C server.
Apple will probably fix this vulnerability soon. In the meantime, the Apple app screeners will probably be on the lookout for any apps being submitted that may want to exploit this vulnerability. This is exactly the type of thing that malicious hackers have been looking for. Malicious hackers go where there is rich data that they can use for monetary gain. Right now, there is no richer data to be found than what resides in consumers’ smartphones.
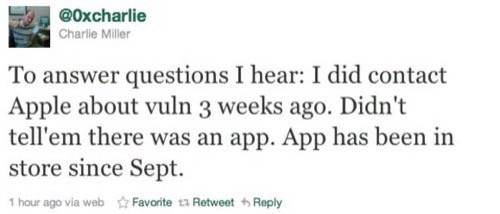
According to his Twitter account, Miller submitted the vulnerability to Apple three weeks ago. The app has been in the App Store since September.
Yes, Miller violated the Apple TOS by knowingly putting an app with the possibility to download malicious code in the App Store. Does he deserve his fate? It can be said that he saved Apple from a world of headache by alerting them to the vulnerability. Let us know what you think in the comments.

















