Search engine poisoning is the most prevalent form of malware delivery on the Web, according to the security researchers at Blue Coat. In its 2011 Mid-Year Security Report Blue Coat outlined the biggest threats to Web security and the attack vectors that malware providers are using to infiltrate users’ computers.
Search engine poisoning (SEP) makes up 40% of malware delivery vectors on the Web. The practice is when malware and spam attackers inundate search results with links to bait pages that will take users to malicious websites that will download malware to a computer. Spammers reach higher in search rankings by creating link farms that drive their poisoned pages further up search results. People want to be able to trust that what they search for in Google, Bing or Yahoo is safe to click on. Users are not conditioned to think that search results could be harmful to the health of their computers. The other leading attack vectors on the Web all pale in comparison to SEP, with malvertising, email, porn and social networking all 10% of malware delivery.
The Dominance of SEP
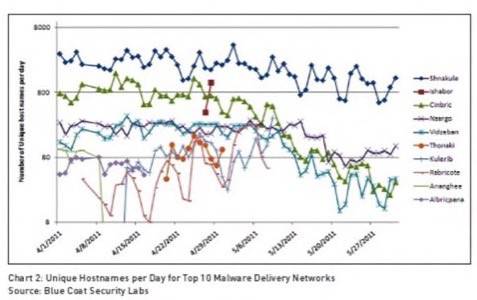
Google and security companies are in a giant game of whack-a-mole with the malware creators, said the head of Blue Coat’s malware research team, Chris Larsen. The botnet networks that create malware are constantly shifting and their delivery mechanisms grow evermore sophisticated.
Yet, SEP attacks do not fundamentally change, they just evolve. As an example, Larsen points to the killing of Osama Bin Laden and the mass of searches that were created the day after the announcement was made to the world. The malware creators used their existing infrastructure, changed the signatures of the command-and-control servers and unleashed a mass of bait links onto the Web.
Malware attackers have come to recognize that users are more wary of clicking on suspicious links that promise something unbelievable or outrageous. So, the vector is shifting to image search. Images are much harder to guard against and have proven to be fertile soil for malware providers. It is harder for Google and the security companies to find the “link farm” that creates the poisoned search results in images.
Porn, Malvertising and Email Remain Strong
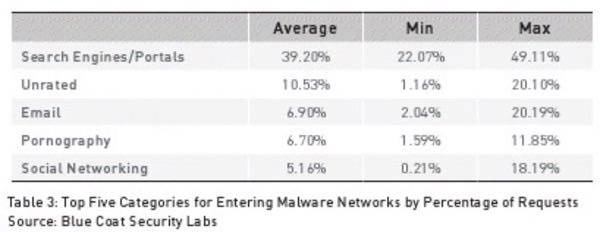
In the table above, “unrated” includes malvertising – the practice of poisoning ads on the Web that lead to “bait pages” in much the same way as SEP does. The Blue Coat report notes “people like to look at other people and human nature is unlikely to change.” There have been spikes of up to 11,000 new porn sites a day, which makes the need for real-time Web defense systems tantamount. Yet, porn as a delivery vector has actually fallen in Blue Coat’s rankings, falling behind email since the last report the company issued in February. Symantec reported last week that email spam was at one its lowest level since 2008 so it looks like the overall amount of malware on the Web may be decreasing.
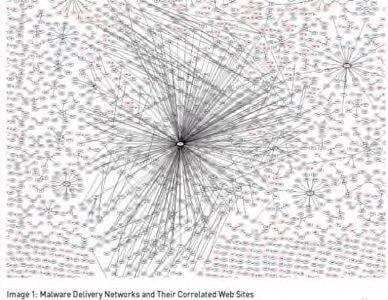
Larsen cautions that might not be the case. Malware vectors are cyclical by nature. The changing nature of botnets make it difficult to determine exactly how much malware is being driven from what sources. Botnets are becoming more difficult to identify and are increasingly sharing (or simply overlapping) resources. On one hand, the more sophisticated the botnet, the harder it is to dismantle. Yet, Larsen thinks that the more complex botnets become, the more vulnerable they become.
The Changing of Botnets
“The network is constantly changing,” Larsen said. “The bigger the attack surface, the more vulnerabilities are created in their own networks.”
The Web is a large, complex place made up of many different standards and approaches. Hackers take advantage of this complexity by exploiting weaknesses in portals that are not secure. Larsen thinks that the more complex botnets become, the more portals are opened where security companies can worm into the networks and take them down.
Botnets are also beginning to share nodes on their networks. According to the report; “Many botnets are known to intersect and share their compromised nodes in a symbiotic relationship (which they do with more monetizable malware such as ransomware, pharmacy spam, scams and a variety of other exploits). The samples analyzed, sandboxed, researched and studied by Blue Coat Security Labs exhibit this characteristic.”
In terms of malvertising, attackers are learning that patience pays. Malvertising networks will lay low within a legitimate ad network and develop clean reputations by passing multiple malware security sweeps. When the sleeping malvertising network awakes it will change the way it operates to deliver the users to a malware host. The next day the malvertising network will be gone, hiding somewhere else on the Internet.

















