Swiss researcher Nicolas Seriot claims it’s possible for “rogue” applications to make their way into the iTunes App Store where they could then be used to steal personal data from victims’ iPhones. According to Seriot’s research, the problem has to with Apple’s lax approval process for applications as well as a flaw in an iPhone security feature that provides access to more data than is necessary. If a malicious application was installed on someone’s iPhone, it could use this loophole to quietly harvest personal data including phone numbers, address book information, the phone’s unique identifier and more. Then, using the phone’s Internet connection, it could send that data back to remote servers, all unbeknownst to the iPhone’s owner.

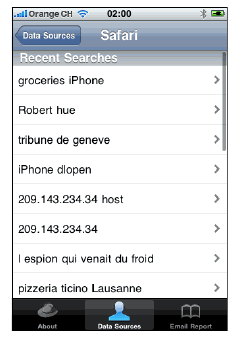
In his speech at this week’s Blackhat security conference in D.C., Seriot demonstrated how an attack such as this would work. Using a proof-of-concept application he dubbed “SpyPhone,” he was able to retrieve the 20 most recent web searches, YouTube viewing history data, keyboard cache, phone number, and email account parameters including the email address, host, and login information (sans password) from an Apple iPhone.
Introducing “SpyPhone”
The SpyPhone application works because of what Seriot considers a security flaw in one of the iPhone’s “sandboxing” mechanisms. On the device, installed applications are prevented from reading each other’s data or accessing specific locations, such as the Music Library, for example. However, they are still able to read the data contained in a number of system and application preference files where personal data is contained.
This illegally harvested data could be retrieved by a malicious application and then sold on the black market to identity thieves or could simply be used for spying purposes. Some of Seriot’s examples of the possible dangers are a bit far-out though, as they have him imagining the attackers using the data for everything from blackmail to robbery to virtual stalking.
In addition, as pointed out on the Mac Security Blog, any computer application has access to some information on the system on which it’s installed. Besides, allowing iPhone applications access to things like your address book is considered a feature, not a bug. The real problem is that users may or may not be aware of what an application has access to and what the application is doing with that information.
According to Elinor Mills at CNET, some developers have already abused their access to this personal data. both intentionally and unintentionally: “A game called Aurora Feint was uploading all the user contacts to the developer’s server, and salespeople from Swiss road traffic information app MogoRoad were calling customers who downloaded the app,” she says. “Game app Storm8 was sued last fall for allegedly harvesting customer phone numbers without permission, but it later stopped that practice. And users also complained that Pinch Media, an analytics framework used by developers, was collecting data about customer phones.”
However, to date, there have been no reports of the collected data actually being used for nefarious purposes.
What Can Be Done?
To protect yourself from these sorts of threats, Seriot recommends iPhone owners clear out their browser’s search history regularly, clean the keyboard cache in the phone’s Settings and remove or change the phone’s declared phone number.
He also recommends that Apple introduce security features that would allow users to opt-out of having usage data sent from their iPhone back to developers’ servers. Applications could also be further locked down to the point where they would have to ask permission to access your address book.
At the end of the day, though, there’s really no way for consumers to know for sure what their applications are doing. Still, the risks of using an iPhone aren’t significantly greater than those involved with using a computer. What consumers should take away from all this is that privacy isn’t guaranteed when going online – whether that’s on a laptop or via a web-connected mobile application.

















