This is a follow-up to our earlier post on RFID and rustling. This is the first draft of a blueprint for a grassroots method a rancher could use, free of federal involvement, to employ RFID against rustling. This is not the finished product.

Federal livestock-tagging systems have been tried before, most prominently in the wake of the mad cow disease scare. They have all been disastrous. Ranchers disliked the perceived imperiousness of a top-down implementation and resented the expense. Distrustful of federal authority, which has resulted in high-handed dismissal of ranching concerns at times, the centralized nature of a national data bank was also rejected. Organizations that do not exist on the federal level have also tried to encourage a centralized tagging protocol. The same issues inhered.
We identified an issue that was of concern to ranchers alone and which was not being dealt with efficiently by anyone: rustling. Since the economy has tanked, cattle rustling has become popular again among the rural criminal classes. Remote areas, especially in the west, reduced law enforcement due to budget cuts and other issues have resulted in success for rustlers and pain for ranchers. We figured that RFID, implantable tracking devices the size of a grain of rice that use radio frequency codes, would be very popular. But, given the aforementioned top-down, centralized nature of government thinking and previous experiments, it is not being used to track missing cattle. In our previous article we noted first that it would never gain ranching support until those issues were removed, then we decided to create the blueprint for such a system.
This is the start of that blueprint for a self-administered, grassroots livestock tagging strategy that is rancher-guided and designed specifically as an anti-rustling measure.
The guiding motto of our strategy is this: THE RANCHER OWNS HIS OWN DATA.
There is no exception to this. Each rancher owns his, and only his (or her) own data. Government authorities are not and never will be involved in, or have access to, a given rancher’s data of their own volition. In fact, no one but the rancher has access.

Ranching in the Cloud
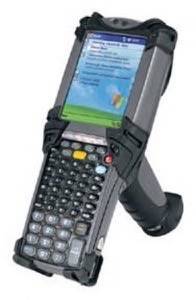
In our system, the rancher, and only the rancher, decides that he wishes to tag his cattle. If rustling is a problem and the rancher decides the expense is worthwhile vs. losing X number of cattle at $1,000.00 a head, he sets himself up. The expenses will include buying the chips, tag inserter and scanner (we do not endorse any manufacturer), and maintaining a personal computer and Internet connection.
The RFID tags are inserted on the rancher’s property, by either a ranch employee or a vet. The frequencies that the RFID chips produce are set by the rancher. Those frequencies are recorded by the rancher on his own computer, temporarily.
The lists of “correlations” (I term we’re using that means which cow belongs to which frequency) will not reside on the rancher’s personal computer, nor on a government server or a commercial server. It will, instead, reside in “the cloud.” When using cloud computing, the rancher saves data onto, and only he can call that information back out of, the Internet. A protocol decides which servers will contain which packets of data. These packets are not like paragraphs or discrete pieces of information like a given RFID frequency, but rather the coding that eventually comes together to make a word or a number appear on your screen.
Cloud computing is analogous to an electrical grid. When you flick a light switch, the electricity that lights your kitchen does not necessarily come from the nearest source, nor all from the same source. A variable set of instructions decides on the spur of the moment – and with no way to tell beforehand – which sources are free to hand you your power. Imagine the same thing with your information. Can someone “download” or otherwise capture your information? No more than they can capture the light that comes out of your nightstand lamp.
You may be buying online storage from a specific company, much in the same way that you buy electricity from a single electrical company, but they do not have your data in boxes where they could be seized or otherwise compromised.
This will make it impossible for a rancher’s information to be seized or intercepted by anyone.
Self-RFID vs. Rustling
Let’s say a rancher has 500 head of cattle. He injects each cow, sets the frequency and scans it. He attaches a description of the cow to the frequency, enters this correlation in a spreadsheet and uploads it into the cloud. Additionally he positions RFID wands at the pinch-points on his spread the closest to access necessary for the trailers a rustler might use or a trailer a rustler would have to use to herd the cattle out of the rancher’s area.
Several months go by and the rancher notices several dozen cattle are nowhere to be found. He suspects rustling. He checks the stats on his pinch-point wands [tech]. He investigates possible places that cattle might be. If his own investigation does not turns up the missing head, he sends a list of RFID frequencies that belong to the missing cattle to people of his choosing. He is the agent of the sharing of this information and he sends it only to the people he trusts. These may include local law enforcement, cattleyard administrators and buyers. If anything turns up on the wands, he might also communicate the possible point of egress for the cattle.

The most likely people for a rancher to contact would be local law enforcement, cattleyards and fellow ranchers. If a law enforcement authority found an individual engaged in suspicious actions, loading up cattle in an odd place for instance, normally the person would direct the officer’s attention to the brands. Brands, however, prove nothing. They are easy to fake. But if the officer knows an area rancher has been rustled, he can scan the cattle in question. If the RFID scans match, the officer has the stolen cattle and probably the rustler. The same thing can be done by a yard owner when the cattle seem off. A fellow rancher can scan stray cattle or scan cattle being offered to him for sale. Again, if the RFID frequencies match, the cattle are found.
In the event that the information becomes part of a court case, it is merely the frequency, and the record the rancher made of that frequency’s relationship to a certain cow, that is in possession. The rancher can go straight home after recovering cattle, change the frequency and upload the correlation into the cloud. Even people who had access to the previous correlations could make no use of it to identify specific cattle, again, until the rancher who owns the data makes that decision.
Preservation of individual initiative and data ownership

This system ensures a number of things.
No one but the rancher owns and can manipulate cattle data
The data cannot be seized
Cooperation with anyone else is at the discretion of the rancher
The information the rancher records is decentralized
The rancher can keep track of his cattle and use that information to catch rustlers
An experienced computer security expert once said that if a party has infinite time and never-ending money, they can crack anything. The key idea there is infinite and never-ending. No party, including a government, has time and money in those proportions. But all they really need is enough of them to defeat the steps you have taken to guard your data. Conversely, all you really need to do is make sure your methods are two steps beyond what they are willing to do. Then, you own your own data.
That’s it, brothers and sisters. It’s not a final draft, it’s a step. We welcome all input as we refine it. We especially look forward input from ranchers, manufacturers of the equipment mentioned and cloud computing types.
Thanks to Kin Lane for contributing his technical know-how and research skills for this article. That said, he’s not to blame for it.
Photos of Warm Springs Reservation in Oregon and San Juan County in New Mexico by @thinkyiddish

















