Every time a botnet is taken down, another is waiting in the wings to take its place. Each successive iteration of malware infected networked computers is more sophisticated than the last. Security research company Kaspersky believes it has found one that is almost indestructible.

The TDL-4 botnet is 4.5 million PCs strong. It has some unique features that make it difficult to remove such as a powerful rootlet exploitation and the ability to disable other malware that is installed on a computer. Those features make it difficult to detect and remove the malware, but that is not what makes the botnet indestructible. The way TDL-4 communicates with its command-and-control center and other infected computers is what makes it unique.
Using Encryption to Hide
Users usually think using encryption to transfer data and messages is a good thing on the Internet. In general, it is (despite the headaches associated with implementing and maintaining HTTPS). TDL-4 uses encryption against security defenders by swapping the table created for outgoing HTTP requests and eventually converting it to HTTPS using Secure Socket Layers (SSL) to connect to the command-and-control server.
Here is how the Kaspersky team describes the process:
“This table is activated with two keys: the domain name of the botnet command and control server, and the bsh parameter. The source request is encrypted and then converted to base64. Random strings in base64 are prepended and appended to the received message. Once ready, the request is sent to the server using HTTPS.”
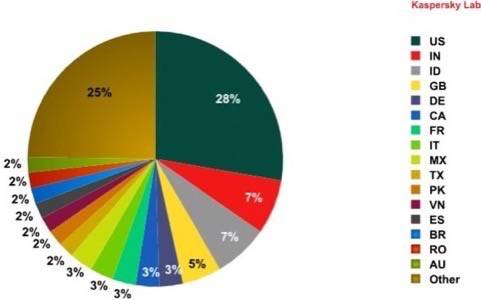
Here is Kaspersky’s breakdown of the 4.5 million infected computers:
Essentially, TDL-4 uses peer-to-peer networking that enables it to hide the command-and-control center and also move the server so that it does not have one centrally-identifiable location. It encrypts the P2P communication, making it nearly impossible to track.
The Malware That Kills Malware
In the wild, only the strong survive. TDL-4 recognizes that it is stronger than its competitors, but also the fact that its competitors’ behavior provides a threat to detection.
Botnet malware doesn’t want the user to know that it is hiding in the hard drive. That means digging deep into the rootkit and kernel of the machine and tricking the rest of the system that everything is just fine. Yet, less sophisticated malware has tell-tale signs that it has infected a user’s device such as unusual packet bursts, slowing of the machine and general odd performance issues.
So, TDL-4 kills the competing malware. The malware is a bootkit that accesses a computer’s MBR (master boot record). It does this to hide from security programs and increase the life-cycle of the malware. The TDL-4 code, known as TDSS, has the ability to delete the most common viruses found on a computer, such as Zeus. It then downloads its own malware, such as “fake antivirus programs, adware and the Pushdo spambot,” according to Kaspersky.
Unique Behavior
P2P botnets are increasing and the evolution is making it harder to track and destroy the networks. TDL-4 uses a unique method – it uses a public KAD P2P network to send and receive queries. This helps the botnet stay decentralized while also acquiring new devices that are using KAD to share files and applications.
TDSS also works to “poison” search engine results and advertising networks, creating proxy affiliates that can help download the malware to computers. We will have more on malware using P2P and “search engine poisoning” next week.

















