Those looking to avoid the National Security Administration’s prying eyes have new ammunition thanks to Edward Snowden. A report in Der Spiegel has revealed which programs regularly deter the NSA and which ones pose no threat.
According to the report, the NSA was still having trouble deciphering several different types of encryption in 2012. One NSA document reported “major problems” following subjects who used the Tor network to browse the Web anonymously. Other difficulties included cracking PGP encryption, OTR chat encryption, encrypted email providers like Zoho, instant messaging service CSpace, and voice-over IP service ZRTP. The best way to thwart the NSA, apparently, is to use a combination of the above, which results in a “near-total loss/lack of insight to target communications, presence,” the document said.
See also: The Real Lesson From Recent Cyberattacks: Let’s Break Up The NSA
However, the NSA does not find every service so formidable, the documents revealed. The NSA can easily monitor Facebook chats and decrypt the Russian mail service “Mail.ru.” Virtual private networks also seem defenseless; one of the documents described a process by which the NSA would survey 20,000 supposedly secure VPN connections per hour.
Security experts agree that the most disturbing part of the report is the fact that the NSA has found a way to circumvent HTTPS, which secures connections between websites and browsers. HTTPS is used to authenticate a website and protect against eavesdropping, but now its true security needs to be called into question. The document outlined the NSA’s plans to intercept 10 million HTTPS connections per day.
See also: The Tor Project Still Doesn’t Know How Authorities Compromised Its Anonymity
Even more alarming is that, since this report describes the NSA’s efforts in 2011, it is possible that the organization has far exceeded its abilities since then. We know for sure that authorities—possibly including the NSA—are now able to decipher Tor decryption. What the report really reveals is that we’re not as safe from anyone’s prying eyes as we thought.
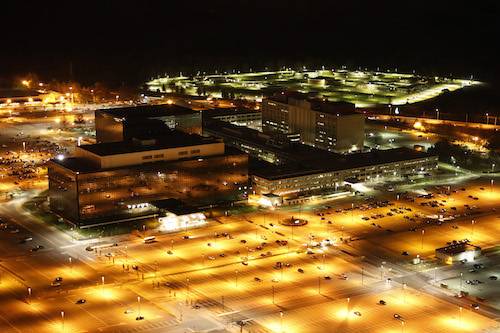
Photo of NSA headquarters by Trevor Paglen

















