Until Microsoft discloses – and patches – a new Word vulnerability on Tuesday, anyone using Microsoft’s Outlook email program and its Word word processor should be even more cautious than usual.
That’s because one of Microsoft’s security bulletins for December includes a “Critical” vulnerability for Microsoft Word, one of the few times Microsoft has attached the “Critical” tag to a Word issue.
Waiting For Patch Tuesday
Microsoft’s standard practice is to give a heads-up on the number of vulnerabilities it plans to fix on “Patch Tuesday,” the second Tuesday of every month. On that day, Microsoft releases the patches themselves, and discloses the vulnerabilities that they fix. (If it revealed the problems before providing the solutions, of course, black-hat hackers could exploit the hole.) So at this point, we don’t know what exactly what problems the current, unpatched version of Word hides.
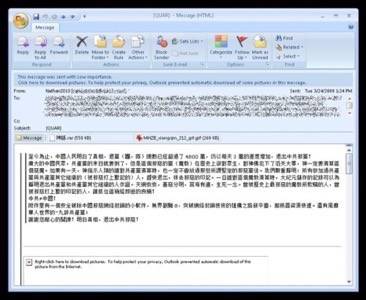
In October, however, Microsoft disclosed a hole in Microsoft Word 2007 and Microsoft Word 2010 that allowed an attacker to take over a PC just by viewing an infected RTF file. That was a significant vulnerability; most modern attacks are triggered when a user views a Web page, or at least clicks a link. The October vulnerability was much more passive, and could be triggered just by idly scrolling down your inbox. Once your machine was infected, the attacker would have the same administrative rights as you do – and if you run as administrator, the attacker could completely control your machine.
Tuesday’s vulnerability appears to be even more severe: It can target Office 2003, 2007 and 2010, as well the Microsoft Word Viewer and Compatibility Pack. As security reporter Fahmida Rashid notes, it’s a good bet that the inclusion of “Word Viewer” means that the new vulnerability allows a similar, passive attack. But note that it does not include Office 2012, so if you own a Surface tablet with the latest Office version, you should be safe.
In total, there are seven updates, which will even ensnare Windows RT. The Windows RT update will be provided by Microsoft, either via the Windows Store, Microsoft Update or Windows Update, a Microsoft spokeswoman said in an email.
How To Defend Yourself
At this point, Outlook/Word users can do several things to help mitigate the threat of any vulnerabilities.
First, always – always – allow Windows to download its approved patches. It’s probably best to allow Windows to install them, too, although users who leave their PCs on, as I do, risk getting caught by an unexpected reboot. While this shouldn’t be a problem for Word users, the inability of modern browsers to “save” inside a Web service can play havoc with your workflow. So it’s up to you whether you want to install the patches automatically.
Second, turn your caution up a notch. At this point, most Web users have a finely honed sense of what is spam and what isn’t, and are able to detect most phishing attempts (misspellings and malformed URLs are common clues). But for now, you’ll have to try and detect whether or not an email is malicious from the subject line. Users and companies who rely a Web-based version of their email (like Google Apps) may have an advantage here.
Third, never run in admininstrator mode. Yes, not having admin rights can be a pain sometimes. But if an attacker can gain the same levels of administrative rights as you can, downgrading your own status to a user might help offer at least a bit of protection.
(Fourth: Get a Mac. There, are you happy?)
It’s not clear that there are, in fact, any worms or attackers with live code exploiting this in the wild. But there almost certainly will be starting on Tuesday, when Microsoft reveals the exploit and the patch and attackers hope to catch complacent Windows users napping. Don’t be one of them.
Image source: Flickr/davef3138










