It isn’t easy to imagine working without technology. Whether it is during work hours or in free time, technology has been rooted in our daily activities which we perform.
The same goes for the HR sector. It is no more just administrative work; it has placed itself in a strategic position to drive the growth of organizations. HR Software Development has revolutionized how the business manages the HR tasks earlier compare to now.
Technology is the key thing that has changed how the HR sector works. Advancements in HR Software Development have enabled automation in work processes that were earlier done manually.
Recent Trends in HR Software Development
- However, innovations in technology also carry challenges with them. Data security and privacy have been hot topics nowadays. Governments worldwide enforce strict rules and regulations to ensure people’s data are protected and not misused.
- Technology is not just limited to engineers and programmers. Every employee in all departments is dependent on technology to do their job. Everyone needs to have a basic understanding of privacy and security
- According to a report published on Financial Express, small businesses are the primary targets for cybercrime gangs. Small companies prioritize how to make profits and expand their business, leaving cybersecurity in a vulnerable spot.
Identifying Key Data Security and Privacy Challenges in HR Software Development
-
Remote Working Conditions
Employees working remotely need to ensure they do not connect to unsecured internet. During COVID-19 as Work from home replaced offices, such incidents occurred more frequently.
Connecting to public Wi-Fi could be risky, leading to the leak of sensitive information like personal mobile numbers, employee data, etc. HR professionals should ensure that employees take precautions while working out of the office.
-
Third-Party Integration Services
Businesses integrate HR software with other systems for various requirements. It is useful for businesses in day-to-day operations. However, it also increases data exposure. While selecting third-party integrations, organizations should ensure they are selecting trusted vendors and following data transfer protocols.
-
Timely Data Removal
Holding unnecessary data is not wise and increases the chances of unauthorized access. Organizations should implement data deletion policies to safeguard employee information.
-
Risk of BYOD
As more and more employees desire to use their own devices, companies implementing Bring Your Own Device solutions are on increased security risks. There is always a fear that others could leak sensitive information about payroll and benefits, exposing employees’ data to other organizations.
-
IoT Solutions
Even if the company’s system is secure, hijackers can access sensitive information in real-time through the Internet of Things (IoT). In these cases, The hacker need not even gain access to the cloud.

-
Damage to Reputation
The first thing that comes to mind when such an incident occurs is loss of trust. The breach effect not only affects the organization but also extends outward. Clients could terminate or withhold the projects if the situation becomes out of control.
Skilled employees could resign from the organization leaving a shortage of talent. Thereafter, even new employees would not want to join the company due to the loss of trust.
-
Penalty Imposed by Regulatory Bodies
Organizations failing to meet security norms not only tarnish trust but also face the wrath of regulatory bodies. In Western countries like the US and European Union, where data security norms are strict, companies have to pay a lump sum amount as a penalty.
Companies have to incur expenses related to lawsuits filed by government officials or even employees affected by data breaches. These result in additional burdens for the company.
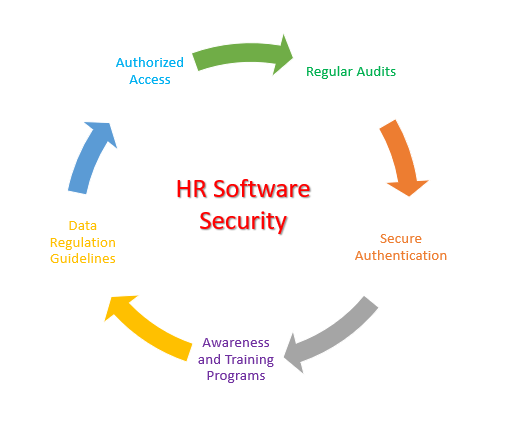
Strategies that can Ensure Data Security and Privacy
-
Conducting Awareness and Training Programs
HR should hold awareness programs to educate employees about various security risks that they should take care in mind while they are not in offices. Employees who do not have much technical knowledge should be explicitly addressed.
This is one of the main tasks to be performed, as according to a study conducted by the World Economic Forum, around 95% of cybersecurity incidents occur due to human error.
-
Comprehensive Secure Authentication Process
The data should be encrypted with proper authentication methods and a multi-factor verification process. Companies should opt for ISO certification, an internal standard for International Security Management Systems. A framework is created for organizations on how they should manage their information risk and protect important assets.
-
Doing Regular Security Audits
Companies must conduct regular security audits to identify vulnerabilities and pain points in the system. This can help the security team keep updated on any malware or leaks that can be solved.
Updating software is also crucial to ensure bugs are fixed. Hackers try to infiltrate the weak areas in old software codes. Leaving it open is a risky process and can be a costly affair.
-
Being Compliant with Data Protection Regulations
Software Developers should ensure that HR Software should comply with relevant regulatory bodies like European Union’s General Data Protection Region and the US Act like California Consumer Privacy Act (CCPA).
Being on the bright side would safeguard companies from being in legal trouble and create a culture of trust.
-
Providing Access Based on Roles
Organizations should grant employees access to sensitive data based on their roles and responsibilities. It ensures that the data is with the authorized person. Maintaining regular reviews and permissions requires us to maintain data integrity.
Final Thoughts
As time passes, more challenges will continue to occur in HR Software Development. Software Developers need to constantly prepare themselves for new security threats by identifying potential challenges and implementing more robust strategies.
With more people understanding the importance of data privacy, developers should build software keeping in mind the growing importance of data privacy worldwide and the strict regulations imposed by governments.
To grow, organizations should make decisions on profit maximization and the privacy of employees and clients to create long-lasting relationships. Ultimately it will lead to a safer and more secure digital ecosystem for employees, clients, and businesses.
Featured Image Credit: Provided by the Author; Thank you!