Apple now says the attack in which hackers rifled the iCloud accounts of female celebrities for nude or otherwise revealing photos wasn’t its fault. The company calls the incident “a very targeted attack on user names, passwords and security questions” that didn’t involve any underlying vulnerabilities in its cloud-storage service.
That may be so, and we’ll know more as investigations continue. But Apple still deserves a good share of the blame—if not for security flaws in iCloud, then for making it unreasonably difficult for users to protect themselves against attacks on their iCloud accounts.
Apple offers some strong security protection for the Apple ID accounts that provide access to iCloud. But it doesn’t “just work.” [Update: It doesn’t protect everything, either. More below.] And setting it up makes it much easier for you to accidentally lock yourself out of your Apple ID account—forever.
Apple To Users: Two-Factor This!
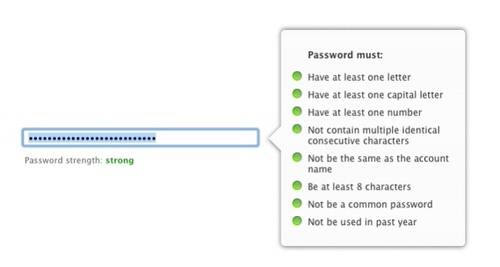
Apple’s statement on the photo thefts contains this standard bit of boilerplate: “To protect against this type of attack, we advise all users to always use a strong password and enable two-step verification.” That’s sound advice, and Apple already requires fairly strong passwords by default.
Apple also offers two-factor authentication, which bolsters security by adding a second step to your login process. Basically, you register a mobile-phone number with Apple; after that, each time you log in, Apple texts you a security code to enter along with your password. (You can also get those security codes via any iDevice that you’ve registered with Apple’s Find My iPhone service.)
This process ensures that no one can get into your account without access to your phone—a pretty good way of ensuring that it’s you entering that password. Trouble is, Apple makes signing up for two-factor authentication way more difficult than it should be. And more than a little scary-sounding, too.
See also: Two-Factor Authentication Is Awesome—Until You Lose The Damn Token
[Update: Turns out that even two-factor authentication doesn’t offer as much protection as it should. At the moment, Apple only asks for an authentication code if you’re changing your Apple ID settings, getting Apple ID support or buying something from iTunes, iBooks or the App Store using a new device. Specifically, accessing iCloud backups via new machines does not trigger an authentication request, though Apple is reportedly testing that feature.]
Start with the fact that Apple doesn’t exactly advertise the existence of two-factor authentication. In its statement, Apple directs people to this knowledge-base page for more information, which turns out to be one of the only mentions of the security method on Apple’s public site. You can also find it by digging around in the settings for your Apple ID; it’s listed under the “Password and Security” tab.
Now the fun begins. Register your mobile number with Apple—and it’s got to be a real number; Google Voice and similar Internet-based phone numbers will leave you hanging—and you’ll get a notification that looks like this:
Seriously, Apple, a waiting period for two-factor #icloud auth?! How does this possibly help anyone? pic.twitter.com/VGTxWlvpAK
— Susie Ochs (@sfsooz) September 2, 2014
That’s right. Apple makes you wait three entire days before it’ll safeguard your account. Even then it makes you come back to your account settings to “continue setup.”
I use two-factor authentication on just about every major Internet service that offers it, from Google and Microsoft to Facebook and Twitter, and I’ve never seen a waiting period like this one. I pinged Apple’s press office for an explanation, but like folks who’ve signed up for two-factor authentication in the wake of the iCloud attack, I’m still waiting.
Looked at one way, none of this is particularly surprising. Apple was, after all, awfully slow to enable two-factor authentication in the first place; Google offered it for two full years before Apple got around to it.
You also have to recall that Apple only beefed up its security following the epic hack of Wired reporter Mat Honan, who lost the contents of his iPhone, iPad and MacBook to hackers who social-engineered their way into his Apple account and wiped his devices. Apple took a lot of heat for that hack, and may have overreacted a bit in order to ensure that no attacker can lock you out of your own account by activating two-factor authentication without your consent.
That said, this setup is a huge disincentive for users and a lousy way to improve account security. People motivated to secure their accounts in the wake of something like the well-publicized iCloud attack could easily have forgotten all about it three days later. Even if they haven’t, signing back into your AppleID account to complete the two-factor setup surely seems less urgent days after the fact.
Now That You’re More Secure—Beware!
Say you’ve waited three days, gotten Apple’s notification and completed the setup for two-factor authentication. Congratulations! You’re more secure.
You’ve also just increased the odds that you could lock yourself out of your Apple account. Permanently.
When you activate two-factor authentication, Apple dispenses with the security questions that are your normal backup for recovering a lost password. It’s an understandable, even a laudable, move on Apple’s part, since security questions are often easier for attackers to guess than passwords. That’s how a college student got into Sarah Palin’s Yahoo email in 2008, and how a California man broke into the email accounts of more than 3,000 women, after which he posted some of the sexually explicit photos he found on their Facebook accounts. (Security questions may have played a similar role in the iCloud attack.)
Instead of security questions, however, what Apple gives you is a 14-character “recovery key.” Apple encourages you to print it out, make copies and store them safely in your house or office. Small wonder: If you lose your phone and can’t find this key, your Apple account is hosed.
And I mean hosed. As Apple puts it (emphasis added):
As noted above, two-step verification requires at least two of the items below to sign in successfully:
• Your Apple ID password
• Access to one of your trusted devices
• Your Recovery KeyIf you have permanently lost any two of these items, you will not be able to sign in or regain access to your account. You will need to create a new Apple ID. You can do so on one of your devices or on the web at My Apple ID.
If you’re the kind of person who can file away a recovery-key printout and have no fear of finding it later when you need it, this shouldn’t bother you at all. For anyone else, though, the prospect of losing your app-purchase history, iPhone backups and photos, and possibly email might be unsettling—even terrifying.
You might even consider it reason enough to avoid two-factor authentication altogether. Which was surely not Apple’s intent in setting up its security system this way, though it may well have been an entirely foreseeable outcome.
Updated 10:35am PT with more information on what two-factor authentication does—and doesn’t—protect.
Lead image by Ivan Bandura; screenshots by David Hamilton for ReadWrite
















