We live in a cyber-vulnerable world – a world governed by data. Data encapsulates almost every aspect of our personal and public life. It is heavily shared, distributed, stored and accessed, and it is constantly at risk. Recent mega-hacks, such as the ones on Target, Yahoo, and Ashley Madison, among others, demonstrate that leaking of personal information and misuse of our data are inevitable in a world that is becoming increasingly more connected and data-centric.
As concerning as these hacks are, we should be aware that at the end of the day, the risk is merely the misuse of data. Without question, attacks such as these can have devastating effects on people’s lives, but their outcome is limited to the virtual world and cannot touch the physical world, at least not directly.
See also: The U.S. VA protects your hacking cough from hacking
This is all changing now as our world is gradually developing into a cyber-physical one. Wikipedia defines a cyber-physical system as one where physical and software components are deeply intertwined. That is, physical systems control, and are controlled, by electronic components.
A good example of a cyber-physical system is a modern car, with approximately 60% of its costs associated with electronic engineering. There are often more than 100 electronic units in a modern vehicle that affect critical mechanical and physical components, such as brakes, the steering system and the door lock mechanism.
Another example is a manufacturing plant that is not only monitored by software, but to a large degree, is also controlled by it, often via remote wireless interfaces.
These are only two examples, but many others exist in countless industry verticals, such as intelligent transportation systems, medical devices and home automation — aka the smart home.
Not the same as IoT
A cyber-physical system is closely coupled with, but is not synonymous with, the Internet of Things (IoT). IoT devices are typically the controllers of the cyber-physical domain. They use one or multiple connective technologies (e.g. cellular or Bluetooth) and are governed by service providers or user applications on a mobile device. For instance, the iPhone application provided by your vehicle manufacturer enables you to unlock your car or start the engine remotely. The Amazon Echo smart speaker app that controls your home lighting is another good example.
What is common to these examples is that they allow us, as end users, to wirelessly manipulate physical functions.
Our control over these systems is terminated at the IoT controller (the vehicle telematics system or the smart speaker, respectively). The IoT controllers communicate with physical objects using two key elements – sensors and actuators. Sensors measure properties of the physical world (e.g. the temperature of a centrifuge) and report them to the controller. Actuators manipulate the physical world (e.g. keep the car in its lane) at the command of the controller.
The glue that connects all of this is software in the form of code and data, and it is software, not love, that makes our 21st Century world go ’round. Therein lies the problem – software code inevitably has bugs and design smells, which can potentially lead to serious security issues – what we would call exploitable.
The number of actual exploitable bugs per 1,000 lines of code depends on numerous factors, including what research you care to read. But even by the most optimistic research, the average vehicle, with some 100,000,000 lines of code, is likely to have a few thousand exploitable bugs – that’s what we call a hacker’s paradise.
Before we panic, get rid of our cars and revert to horse-drawn carriages, it is worth noting that cars are safe and that this number does not necessarily represent a few thousand ways in which your car could be manipulated to kill you as you are driving. To truly assess how vulnerable a system is to attack it needs to be thoroughly analyzed. There are many factors to take into account, such as attacker motivation and access to the target. Still, the overall concern is valid, and no less of a valid question is “how did we get here?”
My answer might catch you by surprise. I think that it was almost inevitable that we arrive at this point. History has shown, time and again, that markets are driven by features, with security lagging behind. When the first computers were connected to the Internet, only a handful of experts thought of the issues of its inherent insecure architecture. Of course, they were largely ignored because they didn’t contribute to the bottom line.
The result was that we gradually became acquainted with a world of mystical cyber-creatures, such as viruses, worms and malware. It took time for the industry to react, because it’s always harder to add security to a production environment. Gradually, antivirus programs and firewalls were invented and we managed to move on. PCs are not without their security issues, but the economy didn’t collapse and the sky didn’t fall.
The next wave of connectivity
A similar path could be traced as we moved on to the next wave of connectivity – smart mobile devices and the evolution of IT systems. The security guys are always blowing their whistles at the gate, shouting that we must build in security at the initial design stages, but market drivers are pushing for features, more of them and faster.
Is the same happening in the IoT world? Recent data suggests that this is indeed the case. So, you might be comforted by the premise that we let the dynamic of technology run its course, adding in security as an afterthought, the same way we did in the past. However, there is one very important observation, one which I would like to be the takeaway of this article – the tolerance for error falls dramatically every time we become more dependent on software.
We have managed to overcome loss of data on our personal computers and hacked phones. We struggle with colossal data breaches to credit cards databases and our most personal information. Will we be able to cope with a real mega-hack that compromises, or worse yet, irrevocably harms, our physical world?
A better idea might be to invest in security by design. Those experts might be right this time around.
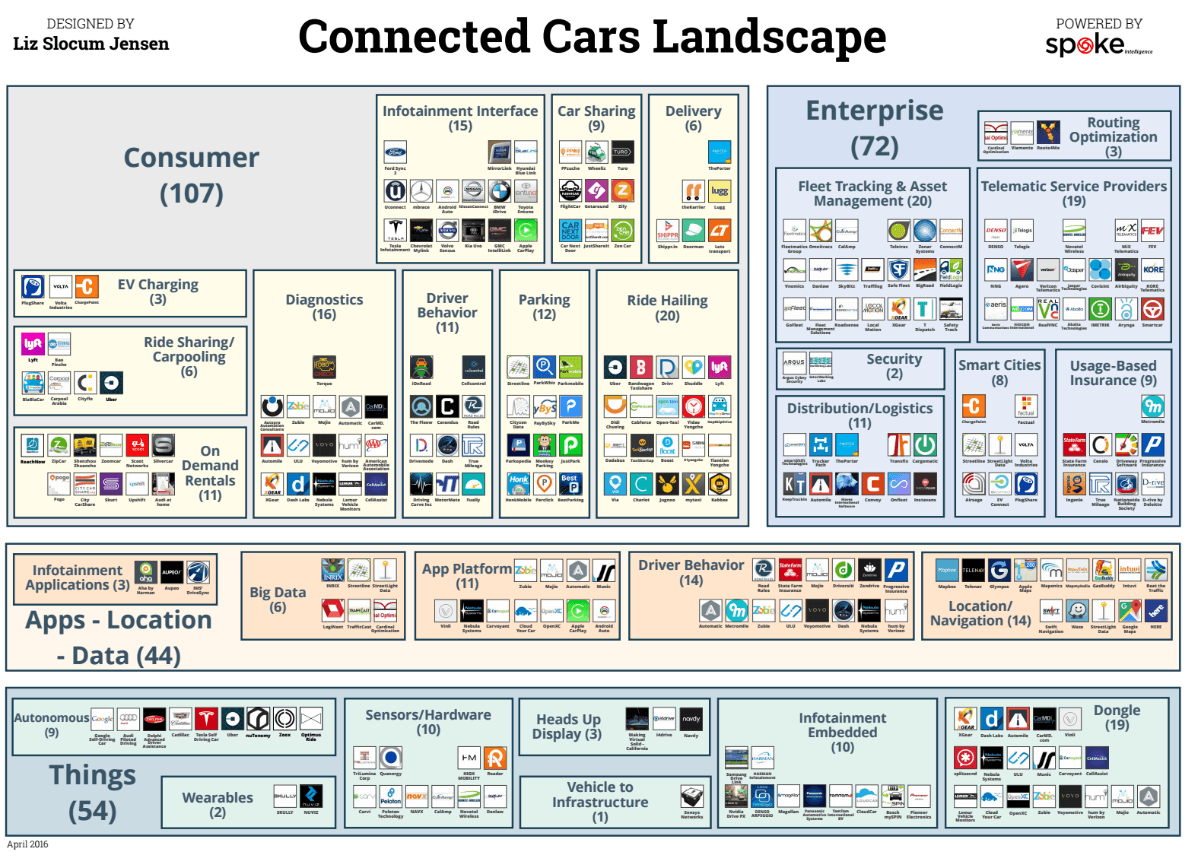
This article is part of our connected cars series. You can download a high-resolution version of the landscape featuring 250 companies here.

















