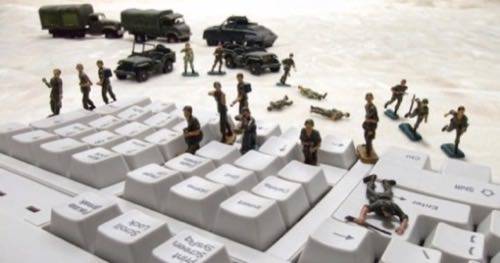
Last week’s call from U.S. Secretary of Defense Leon Panetta for an expanded offensive role in cyberwar activities may have the ring of Hollywood drama, but the real-world implications for U.S. companies could be just as dramatic. Some observers speculate that American enterprises could be conscripted in order to create a coherent national response to cyber threats.
Going On The Cyberwar Offensive
In a speech to business leaders in New York City Oct. 11, Panetta for the first time admitted the U.S. armed forces were prepared to take on an offensive role against any cyber attackers who seek to cause significant harm to the U.S. – or the loss of life to its citizens. Prior to this statement, the military has acknowledged only a defensive stance against such attacks.
Panetta touched on revised rules of engagement (ROE) for cyberwarfare, which the Secretary said were the most significant changes to the nation’s Standing Rules of Engagement in seven years. The Washington Post reports that among those new rules of engagement, “for the first time, military cyber-specialists would be able to immediately block malware outside the Pentagon’s networks in an effort to defend the private sector against an imminent, significant physical attack, The Post has reported. At present, such action requires special permission from the President.”
While the new ROEs are not officially outlined, it is hard not to imagine they would not involve an unprecedented level of cooperation between the military and the private entities who will very likely be targets of such attacks.
“More than anything, there will have to be data collection and data sharing” when a cyber attack occurs, explained Jeff Carter, Chief Strategy Officer of EyeLock. But the price of not doing anything could be enormous. In his speech last Thursday, Panetta brought up the example of a derailed chemical train. While he emphasized the tragedy of any loss of human life, Carter added that just ten minutes of the U.S. financial industry being offline would have far more serious ramifications.
That’s the kind of threat Carter sees coming, as many recent attacks could be seend as a cover for attacks on the financial sector for pure gain, or on other industries to obtain intellectual property for competitive or state-motivated reasons.
How Far Can The Military Go?
Panetta was careful to state that the government would not be monitoring private networks, nor involved in the day-to-day protection of corporate and other private infrastructure. That raises questions about the effectiveness of the defense strategy, let alone the usefulness of an offensive response, since cyber attacks can happen faster than the blink of any eye. Would companies need some kind of “panic button” to alert the military that they were under attack? And if a company were especially tied to some portion of the nation’s infrastructure, such as a power company or railroad operator, would such a system be mandated by law?
Introduction of that kind of legislation could raise very large concerns for IT departments. In the near-term, more regulations are something that many companies resist by reflex, even if they are for a broader good. And on a broader scale, it is not at all clear how much the military (or Congress) could legally compel companies to participate in any sort of cooperative response.
The Third Amendment of the U.S. Constitution, which you don’t hear raised in discussion all that often, explicitly forbids the quartering of soldiers in a home without the owner’s permission. This is a historical throwback to pre-Revolutionary War days, but the logic of the amendment could be extended to cover the intrusion of military assets (read: software) onto private servers and networks.
The Fifth Amendment, so often used as a free pass in incriminating courtroom testimony, has a related clause at its very end: “…nor shall private property be taken for public use, without just compensation.”
Neither amendment, of course, prevents voluntary participation in an active cyberwar program, but fiscal limitations, manpower, or evenethical disagreements might be enough to keep a critical company from joining.
For instance, hospitals and medical centers could be regarded as critical infrastructure. But how would the interface between government and hospital function with HIPPA regulations designed to absolutely protect patient records?
Here Comes The Draft?
Nevertheless, at least one academic paper has argued that companies be drafted to participate in cyberwarfare.
“Cyberwarfare… will penetrate the territorial borders of the attacked state and target high-value civilian businesses,” wrote University of Dayton Professor Susan Brenner in 2011. “Nation-states will therefore need to integrate the civilian employees of these (and perhaps other) companies into their cyberwarfare response structures if a state is able to respond effectively to cyberattacks.
“While many companies may voluntarily elect to participate in such an effort, others may decline to do so, which creates a need, in effect, to conscript companies for this purpose,” Brenner and her co-author, attorney Leo Clarke, added.
Those are just some of the thorny legal issues with which the Department of Defense’s Rules of Engagement for cyber warfare will have to contend.
“The legal and policy entanglement in cyber is far, far more difficult than it is in some of the other domains,” said former Deputy Defense Secretary William Lynn at a 2011 cyber security conference.
Image courtesy of Shutterstock.

















