As anyone who has ever had a valid credit card charge questioned knows, there is a lot of fraudulent use of cards, and the Internet has made it even easier for the bad guys to exploit them. According to comScore, last year ecommerce in the U.S. reached record levels of spending with more than $160 billion in transactions. With all this activity, it is like looking for the proverbial needle in a very large haystack to try to track down fraudulent transactions. But a look into a couple of new fraud detection and prevention technologies shows that perhaps the good guys are making some inroads in this war.
First is the news that MasterCard is working with Silver Tail Systems to map abnormal Web traffic flows on ecommerce sites. MasterCard has its own detection algorithms that handle things it observes across its payment processing network, but this shows that more effort is needed to understand the ways that fraud happens online too. Expect to see more of these partnerships in the years to come.
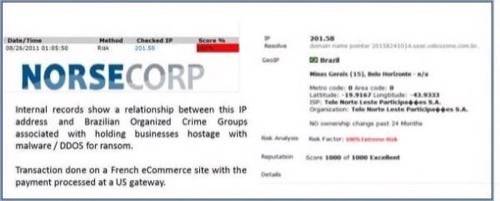
A second company that is working in this area is Norse Corporation, a St. Louis-based company that monitors the Internet looking for fraudsters. Their IPViking customers are the banking and payment processors that want more intelligence about who is buying goods and services online, before the transactions hit the payment networks to be processed.
Norse places millions of monitors around the global Internet, looking for anomalies in transactions that are being attempted on various ecommerce sites. Its approach is similar to what Network Box does for general managed general security exploit detection. Take a look at this transaction, which originated from a Brazilian IP address that has been used in the past to launch denial of service attacks and is associated with Brazilian organized crime. The transaction was done on a French ecommerce site and the payment was supposed to be handled by a US-based processor. Norse caught it in time and the payment was refused.
Here is another example of their intelligent network in operation. They found, over a series of weeks late last year, a set of transactions that originated with Chinese IP addresses using proxy services in Russia, France and China. This means that the originating IP address had been hidden thanks to the proxy. These seemingly random transactions wouldn’t normally be grouped together. Yet all of the transactions were for funeral home services, and appear to be a situation where someone is testing a card number to see if it can be used for more extensive fraud.
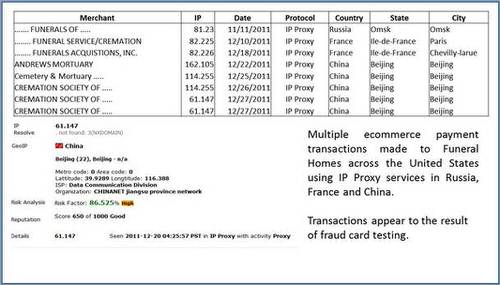
You can see that by detecting these and other patterns, such as a batch of transactions hitting the same ecommerce site within a few seconds of each other (indicating a potential bot net), they can provide a tremendous intelligence to the site owners and help to stop fraud before the transactions are even processed.

















