Cisco released its 2010 Annual Security Report yesterday. The report covers criminals’ slow shift from targeting Windows PCs to targeting other operating systems and devices, the importance of exploiting users’ trust in their social network friends and the rise of Java exploits, and more.

According to Cisco, criminals are targeting social network users more aggressively. In particular, criminals are spending more time and effort trying to steal users’ social networking credentials, since that makes it possible to exploit the trust of all that users’ friends.
Although the exploitation of trust is crucial, Cisco predicts a decline in simple phishing and social networking scams. The company expects instead a rise exploits similar to the Zeus trojan, which steals banking credentials and propagates on social networks, mobile devices and more.

Cisco warns of the “seven deadly weaknesses” exploited by social engineers:
- Sex Appeal
- Greed
- Vanity
- Trust
- Sloth
- Compassion
- Urgency
Even the most savvy users can fall prey to social engineering. For example, Thomas Ryan of Provide Security created fake identity called “Robin Sage.” Ryan was able to get hundreds of government officials and security professionals to friend this imaginary person on social networking sites and, as a result, share personal information with Ryan.
According to the report:
Clickthrough rates for most malware or spam incidents consistently hover at around 3 percent, according to data from Cisco ScanSafe. While 3 percent may not seem high, imagine the impact of repeated waves of spam to which 3 percent of workers consistently respond to and click on. Even this small percentage is the equivalent of having a gaping hole in the network firewall that cannot be closed. Instead of trying to change human behavior, security researchers are exploring the possibility of changing the way we use software to reduce risks.
Java: The New Number One Target
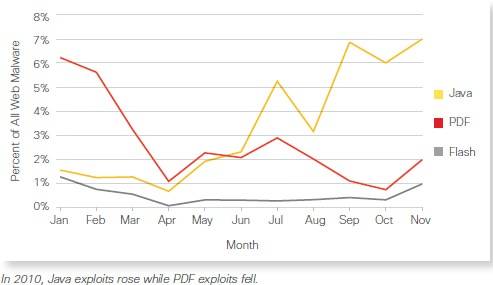
Java and PDF are both frequently exploited, but according to Cisco Java exploits rose last year and PDF exploits fell. Java surpassed PDF as the most commonly exploited technology.
Cybercrime in the Post-PC Era
According to the report, Windows has been so prevalent and so easy to exploit that there was no need for criminals to try to exploit other systems. However, the proliferation of other devices and OSes along with improved security in Windows 7 has changed that.
However, this move is happening slowly. A report from Forrester on security in the post-PC era notes that mobile device OSes are inherently more secure than desktop OSes due to sandboxing. This means that even jailbroken iPhones and rooted Android phones will be harder to compromise than older Windows PCs. However, social engineers can prey on anyone, regardless of the device they are using.
The Cloud: Friend or Foe?
The report cites the cloud as having both benefits and drawbacks for security. The drawback is that data can be intercepted while traveling between a server and the devices that access it. The advantage is that having data stored off-device makes it hard to extract sensitive information from lost or stolen devices.
Money Mules
The report has an interesting section on “money mules.” Once a criminal has stolen a victim’s bank account information, they need a way to get the money into their own accounts without getting caught. Money mules are people who transfer money from a victim’s bank account to a criminal. One way to do this is to transfer money into the mule’s account, then have the mule wire it via Western Union to the criminals overseas. The recipient of the wire from Western Union might not have to provide bank account information to receive the money, making them more difficult to trace.
Some mules are low-level criminals who participate for the money. Others are duped by work at home job ads. Students and people with large debts are often targets.
However, there’s a shortage of mules. “Currently, the ratio of stolen account credentials to available mule capacity could be as high as 10,000 to 1,” says the report.
Winners of the Cybercrime Showcase
Cisco highlights two winners in this year’s “Cybercrime Showcase” – a “good” winner and an “evil” winner.
The Good winner is Thorsten Holz of the security firm LastLine. Holz identified the top 30 servers that the botnet Pushdo/Cutwail used for sending spam. Holz got ISPs to shutdown those servers and, as a result, the rate of spam decreased from 350 billion messages per day to 300 billion per day.
The Evil winner is Stuxnet, which we’ve covered frequently.
What, No Malvertising?
Surprisingly, there is no discussion of malvertising in the report. You can read our post “What You Need to Know About Malvertising” for more about this threat.

















