A series of three independent studies on mobility management and security from Cisco, Mimecast and Good Technology show that managing all this data moving around on laptops and smartphones is going to be a challenge. But you knew that already. But what is clear is that the rate of adoption varies widely, depending on who is doing the measuring.

The three reports include:
- The Cisco 2011 Annual Security Report,
- Mimecast’s survey on business mobility and
- Good Technology’s State of BYOD report.
Cisco’s report is the most troubling of the trio. Gen Y is likely – to the tune of 70% — to ignore promulgated IT policies when it comes to security posture, and a third don’t have much respect for their IT departments at all. To this generation, everything is public, states David Evans, Cisco’s “chief futurist.” (Now that is a job title that I could enjoy.) Granted, “ten years ago, employees were assigned laptops and told not to lose them, and told not to tell anyone their password. End of security training,” as the report states somewhat simplistically, but not far from the truth. Today, things have gotten a little bit better: perhaps there is a self-service website that provisions the laptop, or an endpoint security agent that can manage the device.
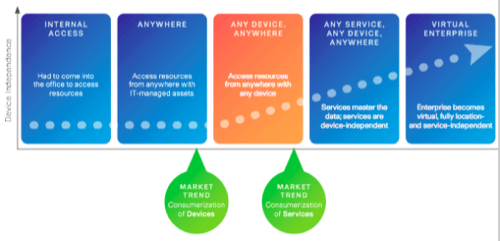
The report describes a somewhat Maslow-like series of stages that a workforce goes through in terms of remote computing access, beginning at internal-only and ending up with the virtual enterprise that anyone can access anything from anywhere, as shown in the graphic below. This last stage is where many Gen Y’ers feel they are entitled to be at when they come to a new job. Nearly a third of them stated in the report that being further down on this hierarchy of access would influence their job choices in the future.
One minor part of BYOD policy-making is being able to filter Web surfing to protect all of an enterprise’s equipment from malware-infected websites. Cisco included a case study that described a nearly three-year program to install its own IronPort security appliances across its entire global organization. The moral of that story is that if it can take so long with Cisco, who owns and makes the technology it needs to protect itself, chances are it will take you even longer. Also included in the report are a series of critical business questions that you should ask your management about BYOD issues and a series of security action items.
Good Tech. found that companies that offer BYOD “stipends” or allowing employees to expense their phone monthly service costs have the highest adoption rates of actually managing these devices (see the bar graph from the report). Half of the respondents are deploying BYOD plans internationally. Since they surveyed their customers at the beginning of the year, the BYOD adoption rate has gone from 60 to 72 percent. This makes sense, given that most of their customers would be on the leading edge of managing their mobile devices. But interestingly, the bigger the company (in terms of staff size), the lower the support for BYOD. The other graph shown from the report show that the density of mobile devices varies among those who have adopted BYOD policies, and not necessarily in any predictable fashion.

Mimecast surveyed 600 IT administrators attending an Exchange conference last month and found that 41 percent of all respondents indicated their company has deployed bring your own device policies. However, the survey also found that small- to medium-sized businesses have been quicker to support employee devices and mobility, compared to larger companies. They found that 28% of companies with 4,999 employees and less support three or more devices, and only 14% of these companies support five or more.
Clearly, we have a long way to go before we can have any device operate with impunity anywhere across our enterprises. The Cisco report is recommended reading, but it might ask more questions than it answers.

















