New Trend: Web 2.0-controlled malware?
Security researchers at Symantec recently uncovered a backdoor trojan whose spread is being dictated by commands hosted in Google Groups, Google’s online discussion forums. The backdoor trojan, named Trojan.Grups, appears to be the first ever malware to use an online newsgroup as the “command and control” center for botnet communications. It’s certainly the first time that Google Groups specifically has been compromised in this way. This new discovery points to what appears to be the latest trend in what you could call “Web 2.0 malware,” that is, nasty computer programs that don’t just spread in social networks, but actually use the infrastructure of the social networks themselves to do the spreading.

Using Google Groups for Corporate Spying
Botnets are groups of computers compromised by malware programs, often called “zombie computers,” which are controlled by “bot herders,” the person or persons responsible for remotely controlling the infected PCs, unbeknownst to the PCs’ owners. Traditionally, a centralized server of some sort would issue the commands that instruct the computers what action to perform. In many cases, the zombie machines are used to send out spam, to perform click fraud, to aid in identity theft, or are directed to attack another web server on the internet, as was recently seen with the Twitter/Facebook/LiveJournal attacks of last month.
With this particular new trojan, the command-and-control center for issuing the botnet commands is not a single server on the internet. It’s Google Groups itself. Using a private newsgroup, the trojan executes a command which logs it into the newsgroup and requests a specific page. The page contains the encrypted commands the malware is to carry out. The responses from the compromised machines are then sent back to Google Groups and are uploaded as posts to the newsgroup.
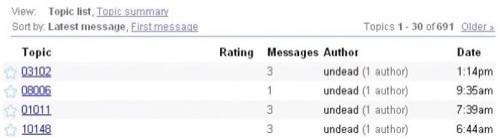
According to security company Symnatec’s analysis of this new trojan, it appears that it is a prototype implementation meant to test the feasibility of using newsgroups in this way. The trojan is attempting to remain discreet and undetected, being used to subtly gather information and potentially determine its future attack targets. The researchers think that the trojan may have been developed for targeted corporate espionage where anonymity and discretion are priorities.
Using Web 2.0 as the C&C for Botnets
This latest trojan isn’t the first to use a social network to aid in its spread. What is unusual about it, though, is that it actually uses the social network that is Google Groups to host the commands which control the malware’s actions. This is a different sort of scenario than your typical social networking-based malware which simply uses popular online networks as the vector for the attack. This is using the network as the brains.
Another recent example of this sort of Web 2.0-controlled malware involves the recent discovery of a botnet which used Twitter.com to issue commands. In an arguably ingenious move, Brazilian identity thieves created a Twitter account for the sole purpose of sending out commands to its associated malware. Each command was posted as a status update to the Twitter account. As researchers noted at the time, this sort of setup could have used any number of web sites or services on the internet to do the same – all that was needed was an RSS feed. In fact, the same malware was later seen on both Jaiku.com, a Twitter-like service acquired by Google in 2007, and Tumblr, a simple blogging platform.
Given the open, “anyone-can-post” nature of Web 2.0 and social networking services, the online communities that have become the de facto standard on today’s web, it was only a matter of time before that openness was compromised by hackers wishing to use the services for more nefarious purposes than just “sharing with your friends.”
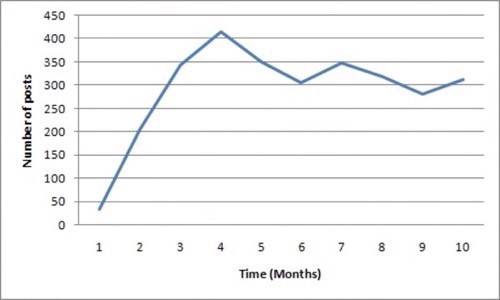
For now, there are still relatively few incidents where a botnet has been discovered as using a Web 2.0 service as the command-and-control center for operations. However, the idea must surely appeal to botnet operators as hiding these sorts of messages in the larger social networking infrastructures that house valid communications makes the botnets harder to identify and shut down. You can’t simply blacklist the IP or URL once discovered – you have to rely on the social networking vendor to remove the malicious accounts. If any of these recent efforts at web 2.0-controlled malware are successful (and the Google Groups trojan has been – it’s been around since November 2008!), then it’s likely we’ll begin to see even more programs like this in the future.