Looking back at 2011, we could call it subtitle it as The Year Of Android Malware. It started with DroidDream and reports have been issued all year that have shown exponential growth in Android malware. It is not getting any better. If Juniper’s research can be believed, it is getting much worse.

Juniper says there has been a 472% rise in Android malware samples since July 2011. Juniper says that almost all of the Android malware contains code for root access that will force the device to communicate with a command-and-control server and download additional instructions. 55% of Android malware acts as spyware and the rise of “SMS Trojans” has become a significant problem.
Recent Jump In Android Malware
Juniper notes that Android’s open market structure, where almost any developer can pay $25 for developer access that can be anonymized, is the primary culprit for the rise of Android malware. Juniper notes that iOS may or may not be any safer but that Apple makes it safer by requiring code signatures and pre-screening all apps. Smart Android publishers put code signatures into their apps because they know that the security applications have the capability of white and black listing certain signatures and that helps them keep their app out of the malware repository that security apps scan for.
October and November have seen the highest growth rates for Android malware samples since the rise of the platform, according to Juniper. The number of samples grew 28% in September, October had a 110% increase over September and a 171% increase from July 2011.
Spyware with root access is the main threat from malicious Android applications. Juniper notes that the vulnerability to root access from malicious apps is prevalent in 90% of Android devices in the consumer market. Outside of spyware, the SMS Trojan makes up 44% of Android malware. Juniper published another post today showing that much of the SMS Trojan activity is coming out of Russia.
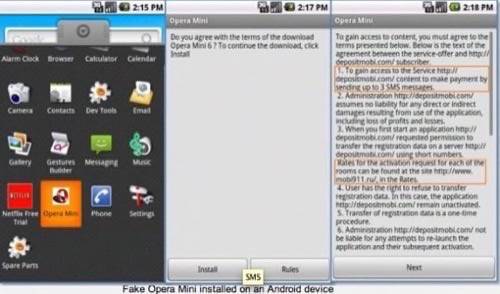
SMS Trojans work by getting users to click on text messages or links in emails that will prompt them to pay for an app through premium text messages. These are often from pirated of cracked apps. The problem is that users end up paying for free apps, like Opera Mini for Android, or developers do not get paid for their premium apps.
How The SMS Trojan Works
Here is how it works for Opera, according to Juniper’s research:
Step 1: User gets a link by text or email.
Step 2: User opens the link within Android but is redirected to a site that tells the user to upgrade Opera.
Step 3: User show a message that brings them to a screen that says to download the browser, they have to pay with three premium text messages.
Step 4: User agrees and texts are sent. This supposedly costs $11 or 338.67 rubles.
Step 5: The fake Opera reveals the URL for the real Opera that is free in the Android Market.
Source: Juniper Research
Check out the infographic below for Juniper’s research findings. Also, remember that mobile security often comes down to common sense. Do not click on malicious links and make sure to read your app permissions.
Does the big, scary red Android scare you? Let us know in the comments.










