Internet privacy solutions provider TRUSTe is concerned that mobile apps do not have built-in privacy solutions. TRUSTe claims that 77% of all mobile applications lack privacy policies that can allow users to decide how they want to share data third parties. As such, TRUSTe is coming out with a free privacy policy for mobile developers later this month.

Essentially what TRUSTe is coming out with is a privacy policy wizard or starter kit for mobile developers that do not have policies in place for their apps. Developers are led through a set of questions defining what their apps do and do not do in terms of privacy and at the end of the quiz, TRUSTe gives them a line of code that links to the apps privacy policy. The free version does not give a developer a certified TRUSTe privacy seal and there is potential for abuse of the system by creating a privacy policy with an app that does not follow those guidelines.
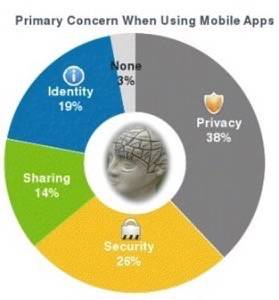
Privacy is a definite concern for mobile users. On the flip side, it is almost an afterthought for developers that are looking to harness actionable data for update, advertising and marketing purposes. What it really comes down to is the permissions that an app has (can it read your contacts, access the Internet etc.) and if those permissions are actually what the app is performing.
To that last point, security vendors such as Symantec, Lookout and Norton check an applications code against its permissions when an app is downloaded. If the app is safe and is doing what it says it is doing, it is fine and the security apps will not flag it. If it is not, it prompts the user to remove the app (to varying degrees between each security system).
The TRUSTe policy for developers is an extension of the system that it has already been offering to enterprises building internal apps. When it comes to privacy, users are concerned with how geo-location (remember the iPhone/Android location tracking issue earlier this year?), whether or not an app has permission to use text messaging and/or a users phone number and contacts list, how and where apps transmit data and how users are being tracked by advertisers. These issues touch on a variety of privacy concerns such as identity and location and, perhaps the most important, users bank accounts.

The free TRUSTe privacy policy is more of a creation wizard for developers. It does not actually enforce any of the claims that the could be created within the wizard. Dave Deasy, VP of marketing for TRUSTe, admits that the new tool does not keep insidious developers from creating apps that violate the privacy policies that are created.
“This solution won’t necessarily keep somebody honest but is rather for developers that don’t know where to start in creating a privacy policy,” Deasy said.
That is why developers using the free version of the policy wizard will not get actual TRUSTe certified seals. The TRUSTe seal is reserved for those that pay for the certification service that provides protection to the user.
What it comes down to for users is: protect your privacy on your own. Look either for the official TRUSTe seal (or other privacy vendors) and use security applications to make sure the permissions your app is telling you it performs are actually the actions it performs. When it comes down to security and privacy, a user can have all the tools in the world to protect themselves but that will not protect a user from making bad choices.
Developers – Does TRUSTe’s new policy generator look like something you will use? What is the opportunity for abuse? Let us know in the comments.









