The same Symantec team that cracked Stuxnet has found new variations on the same theme in packet captures from European networks. They published a blog entry and a full report that analyzes what the impacts of the virus would be, since the exploit isn’t quite a finished product yet, and not all pieces of the exploit have been recovered. It is well worth careful reading.
The team calls what they found Duqu, and it is quite a vile and complex piece of work, as you can see from just one of its components diagrammed by Symantec. They state that its creators must have had access to the Stuxnet source code, not just the binary files. They theorize that its purpose is to find weaknesses in particular industrial process control equipment, although they have not found any specific code to tie it to a particular piece of hardware. The reason they propose this is because the code has been found in organizations that have been involved in the manufacture of industrial control systems. “The attackers are looking for information such as design documents that could help them mount a future attack on an industrial control facility,” say the report.
Included in the exploit are the following items:
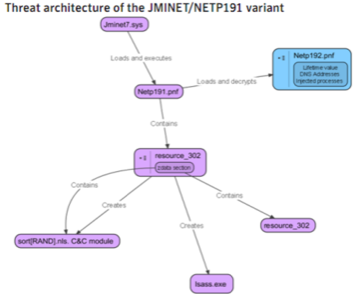
- Keystroke recorder to pick off any passwords,
- remote access Trojan to gain control over any PCs that could be connected to the control equipment,
- Misleading digital signatures: The exploit contains a valid digital signature on one of the driver files, once again calling the need for better signature notaries.
Reading the report is interesting and scary at the same time. Clearly, the team who gained expertise with the creation of Stuxnet continues to learn how to make it better. This, coupled with an upcoming survey that shows that most US small business owners don’t have any Internet security policies or procedures, should give you all some food for thought. That circle of trust seems a bit smaller now.