Twitter can’t catch a break these days. Still reeling from the ongoing denial-of-service attacks that hit late last week (and have yet to let up), the company soon faced yet another threat: the return of Koobface. The Koobface internet worm, a deadly little piece of internet malware which got its start on Facebook, has long since spread to other social networking sites including MySpace, Bebo, and Twitter. But the latest variant – the “new and improved” Koobface – is even more devious than before. And Twitter’s recently launched malicious URL filtering feature couldn’t put a stop to the worm’s spread.

The New Koobface
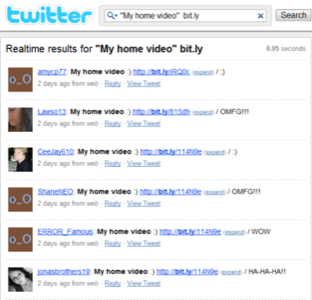
As before, the new variant of Koobface still points users to a fake Twitter page (or a fake Facebook page, if you happened to come across Koobface on the Facebook social network). On the page, users are prompted to download a Flash Player update in order to view a video file. Of course, clicking the link to update Flash actually starts the malware’s payload downloading instead. In order to get users to this point to begin with, Koobface sent out tweets reading “My home video 🙂 [URL].”
Recently, Koobace has ramped up its complexity and is sending out unique tweets that have some sort of random component added to the end of the tweet, with strings like “HA-HA-HA!!”, “W.O.W.”, “WOW”, “L.O.L.”, “LOL”, “;)” or “OMFG!!!”
What’s even worse about the latest Koobface variant is that the landing page for the malware attack was also adding a random component to the URL, allowing it to get shortened to a different bit.ly URL each time a message was posted. As of late last week, security firm Kaspersky Lab had identified nearly 100 unique IP addresses hosting the Koobface worm. They’ve since been able to take the main Koobface site down to stop the current set of attacks, but don’t be fooled – there’s no doubt that it’s only a matter of time before Koobface relaunches with yet another dangerous twist. In fact, that’s been par for the course for this piece of malware which has been attacking social networks since July 2008. Taking down one Koobface vector of attack is like playing a game of “whack-a-mole” – you hit one and another pops up to take its place.
The Real Problem: Short URLs
One of the main reasons Koobface was able to so easily spread on Twitter was due to its use of the bit.ly URL shortener, now the default on Twitter. Not only was Koobface varying its URL to ensure a unique bit.ly link each time, Twitter’s new malicious URL filtering system doesn’t help protect users against pre-shortened URLs.
As we mentioned before, without a focus on shortened links, Twitter’s filtering system is simply not good enough. It’s far too easy to use bit.ly’s website or a third-party Twitter client to shorten a URL before it ever hits Twitter’s web interface to be checked. And naturally, this is precisely what malware writers do. The only malicious URLs Twitter’s current system protects us against are those posted by unsuspecting Twitter users themselves. The bad guys certainly know better and Koobface is a perfect example of this.










